US AI investment in Armenia risks national security vulnerabilities without safeguards against political capture and chip diversion.
When Vice President JD Vance visited Armenia and Azerbaijan last month, much of the commentary focused on the military agreements and diplomatic signals. The more consequential development attracted less scrutiny: Washington’s approval to export next-generation Nvidia Blackwell processors for the construction of Armenia’s first large-scale artificial intelligence (AI) supercomputing center, built and operated by Firebird. This deal is nothing short of an act of geopolitical commitment in a country whose political direction is openly contested and where the surrounding risks have not been carefully enough distinguished. This distinction matters because the two principal risks facing the Firebird facility are structurally different, operate through different mechanisms, and require different responses. Washington should be asking two separate questions: What happens if Armenia’s next government is aligned with Moscow? And what happens if chips are diverted to Russia regardless of who governs?
The Firebird AI Data Center That Washington Approved in Armenia
The Firebird supercomputing center is a 100-megawatt facility expected to come online in Q2 2026. It will be the first project of its kind in the South Caucasus and, on paper, represents Armenia’s formal entry into the high-end global compute economy. The allocation structure is worth examining closely. Twenty percent of capacity is reserved for Armenian entities; eighty percent is contracted to US firms operating in the region. Put simply, this distribution is both commercial and geopolitical. By tying the majority of the facility’s output to American corporate demand, Washington embeds Armenia into US-linked AI supply chains while cultivating domestic capacity. This is especially the case given that the facility sits alongside a broader package of cloud cooperation agreements between Armenian entities and Amazon.
Taken together, these initiatives are designed to position Armenia as a Western-aligned technology hub in the South Caucasus, and to do so at a moment when Yerevan is actively recalibrating its relationship with Moscow. That strategic logic is sound. The question is whether Washington has adequately priced in the political environment in which this infrastructure will operate.
Armenia’s Elections and Constitutional Reform Create Political Risk
Armenia is heading into a June election whose only certain outcome is constitutional change. Prime Minister Nikol Pashinyan has pledged a post-election referendum as part of an effort to secure a peace deal with Azerbaijan and to probably revise the institutional relationship between the Armenian state and the Armenian Apostolic Church. If Pashinyan wins and proceeds along this path, the facility’s operating environment is likely to stabilize. A peace deal with Azerbaijan would ease regional security pressures, potentially unlock transit corridors, and reinforce Western investor confidence.
The more disruptive scenario is an electoral upset. Samvel Karapetian, a Russian-Armenian billionaire, and his newly formed Strong Armenia movement have pledged to rewrite the constitution if they win a parliamentary majority. That pledge carries a specific implication that has received insufficient attention: Karapetian currently holds Russian citizenship, which under Armenia’s existing constitution makes him ineligible to serve as prime minister or as a member of parliament. Constitutional revision could remove that constraint. Washington is therefore embedding high-value AI infrastructure in a country where a credible electoral contender holds Russian citizenship, has pledged constitutional revision in ways that would benefit himself, and has built his commercial fortune substantially within Russian business networks.
Armenia’s Risk Landscape: Political Capture and Diversion
The political capture risk is about what a Karapetian-led government could do to the facility’s operating environment, not through overt expropriation, but through the gradual reconfiguration of the legal and regulatory framework surrounding it.
In fact, a critical legal precedent is already being established by the current government. Pashinyan has moved to revoke the operating license of Electric Networks of Armenia (ENA), the country’s electricity distribution network, which is owned by Karapetian, by invoking Article 60 of the constitution and proceeding to nationalize the enterprise. The justification advanced centers on alleged governance violations, financial irregularities, and energy security concerns.
The merits of these particular claims are not the point. Nor are the potential political motivations of Pashinyan’s team for going after Karapetian’s most valuable asset in the country. Rather, the key point is the legal mechanism that is being deployed. The Armenian state is establishing, in active practice, that privately owned infrastructure can be reclassified as a strategic national asset and brought under state control through constitutional provisions without abandoning formal rule-of-law procedures, and without requiring the kind of naked expropriation that would immediately trigger international arbitration. In other words, a legal architecture for any future strategic asset seizure is being stress-tested right now against Karapetian’s own company.
This, in turn, could set a precedent that would be readily available to any future government. A Karapetian administration, or a successor with similar interests, could apply the same reasoning to other infrastructure it deems strategically significant. High-value AI compute, with its obvious national-security dimensions, would be a plausible candidate. In such a scenario, the threshold question would not be whether such a move is legally conceivable. By deciding to go ahead with the nationalization of ENA, Pashinyan has already answered this.
The implications, however, extend beyond ownership. Effective control over sensitive compute infrastructure depends on personnel access as much as on property rights. Replacing system administrators, maintenance contractors, or executive leadership with actors aligned with Russian commercial interests could introduce exposure at the level of firmware updates and credential management. Shifts in the regulatory environment, including adjusted foreign-ownership safeguards, revised emergency powers, or reclassified security-review thresholds, could facilitate exactly this kind of gradual penetration of operational authority.
In addition, Russia retains additional leverage that amplifies these concerns. Armenia remains dependent on Russian energy supplies, grain, and transit infrastructure. Russia also maintains a military base at Gyumri. In a scenario of heightened pressure, legal mechanisms framed under national-security provisions could be deployed to justify forced partnerships or compelled data access. To be sure, this is not a high-probability scenario, but it is within the range of plausible contingencies that serious risk planning should address.
There is then the all too real risk of diversion, which is distinct from political capture since it does not depend on who wins the June election. Rather, it exists as a background condition under any Armenian government, including the current one.
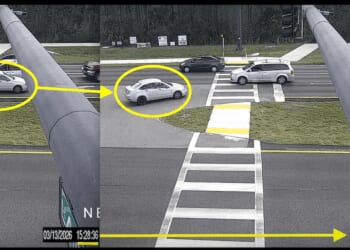
In recent years, Armenia has functioned as one of several conduit routes, alongside Kyrgyzstan, through which sanctioned Western goods have entered Russia. The recent case of Cygnet Texkimp, a United Kingdom-based carbon fiber producer, illustrates the supply-chain opacity involved. UK export authorities suspended shipments to an Armenian buyer, a company called Rydena, following concerns about links to Russian military networks.
Admittedly, Firebird is a US-registered company with no known ties, direct or indirect, to Russia, which limits the analogy. However, Moscow’s formal and informal commercial presence in segments of Armenia’s economy, combined with established smuggling networks, means that the possibility of advanced chips being redirected cannot be dismissed as implausible. The materialization of this risk, moreover, does not require a hostile government in Yerevan. It only requires that private actors with access to the facility’s supply chains have incentives to divert components, and that oversight mechanisms are not sufficiently robust to detect or deter it. Given the scale of what is at stake—next-generation Blackwell processors—it is reasonable to assume that incentives will be there.
What Can Be Done: Protecting AI Infrastructure
Since the two identified risks are different, they each require a separate mitigation framework.
Against political capture, the priority should be contractual and structural. Agreements should include automatic suspension clauses tied to ownership changes in the facility’s governance, constitutional revisions that materially alter foreign-investment protections, or interference with inspection rights. US approval rights over critical subcontractors and key personnel appointments would also reduce the scope for gradual operational penetration.
For diversion-related risks, on the other hand, rigorous end-use verification, enhanced export-compliance monitoring specific to the facility, and sustained intelligence-sharing with Armenian customs and law-enforcement agencies constitute some of the most viable options that ought to be explored by relevant US agencies.
The longer-term solution to both risks is strategic presence via the recently established Tech Corps rather than defensive contracting alone. Embedding American technical personnel, training a local AI workforce to US professional standards, and building durable institutional relationships within Armenia’s technology sector would raise the cost of any future attempt to reorient the facility’s operational environment. Human networks are harder, albeit by no means impossible, to legislate away than contractual provisions. Washington should treat this facility not as a one-time export approval but as the foundation of an ongoing institutional relationship, one that does not depend on any single electoral outcome.
A Test Case Worth Getting Right: National Security Risks in AI Infrastructure
By all counts, the Firebird facility is a meaningful act of geopolitical commitment. However, commitment is not the same as strategic clarity. Washington has embedded high-value AI infrastructure in Armenia at precisely the moment when the country’s political trajectory, constitutional framework, and geopolitical alignment are all in motion simultaneously.
This does not mean that the export approval is a mistake. Armenia’s drift away from Russian dependency is a rare strategic opportunity, and technological embedding is a legitimate tool for reinforcing it. However, the value of this embedding depends on whether the surrounding risks are accurately identified and managed. If Washington manages to articulate the right mitigatory frameworks, Armenia could serve as a model for how Washington uses AI infrastructure partnerships to anchor emerging partners within American technological ecosystems. If it does not, the Firebird facility risks becoming an early case study of what happens when geopolitical and commercial ambitions could potentially endanger national security.
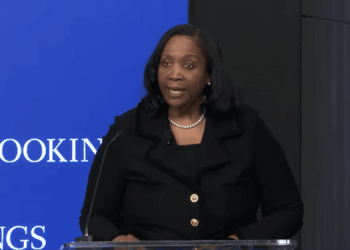
About the Author: Nima Khorrami
Nima Khorrami is an analyst at NSSG, a strategic risk consultancy firm, where he works on Iran and South Caucasus affairs. He is also a research associate at the Arctic Institute. Previously, he has worked at UK Defense Forum and OSCE Academy, amongst others, and has written for a number of publications and think tanks, including MEI in Washington, Carnegie Endowment for International Peace, The Guardian, and War on the Rocks.