A French officer’s decision to use the Strava fitness app while onboard the Charles de Gaulle appears to have inadvertently made its location in the Mediterranean public.
There was a time when the byword in world militaries was “Loose Lips Sink Ships,” a reminder to everyone not to share military secrets. Today, the danger isn’t just what some people might share—although that is still a problem, particularly in the era of social media—but what they might wear!
Such was the case with the location of the Marine Nationale’s (French Navy’s) flagship aircraft carrier, Charles de Gaulle, which was identified when one of its young officers tracked his daily run on the flight deck via his smartwatch.
The issue was that this profile on the Strava fitness app was set to public, and he inadvertently revealed the location of the nuclear-powered warship in the Mediterranean—specifically off the northwest coast of Cyprus. If this story sounds familiar, it echoes a previous incident from just over a year ago that French sailors also provided too much information via the app while logging their runs at the Ile Longue naval base in Brest—the home port of France’s four Triomphant-class nuclear-powered ballistic missile submarines (SSBNs).
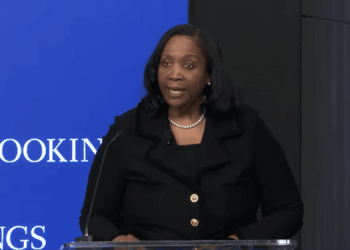
“What keeps happening here is not really about Strava. It is about a much bigger pattern,” said Angeli Gianchandani, adjunct instructor of integrated marketing and communication at New York University and global brand market strategist.
Gianchandani told The National Interest via email that users of such devices need to remember that we are living in an era of “frictionless data generation.”
App Location Tracking Is a National Security Problem
Strava may be a fitness tracker, but it is also a location tracker. One workout route seems harmless, but as it tracks, it then shares that data in ways that users rarely intend.
“Every device we carry, every app we run, and every activity we log produces a stream of information,” Gianchandani said. “Most of it flows outward by default, often without any real understanding of where it goes or who can see it. Aggregate enough data points, and you have something entirely different. Routines, locations, operational patterns. That is not a privacy inconvenience. In a security context, that is an intelligence asset.”
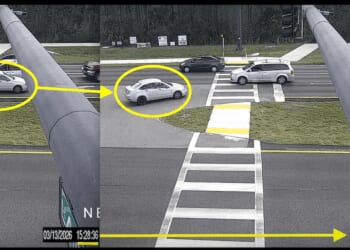
In the case of the aircraft carrier, Strava was able to provide the Charles de Gaulle’s location at sea.
At the Ile Longue naval base, it could help an adversary determine whether one of those four SSBNs was in port at the time—even as the French military understandably may not want such details widely known.
It isn’t just such fitness trackers, either. Ship watchers regularly post about the arrival and departure of warships from ports, and flight trackers report on the movement of combat aircraft. Beyond just tracking movements, sharing online allows the picture to come into focus in a way that wasn’t once possible.
Open source intelligence provides real-time location of military assets.
“What makes this moment particularly consequential is that we have entered the age of open source intelligence at scale. The tools to collect, correlate, and analyze publicly available data—including fitness app data, social media, and satellite imagery—are no longer limited to nation-state actors,” said Gianchandani. “They are accessible, affordable, and increasingly powered by AI with very few boundaries on what can be surfaced or connected.”
Western Militaries Are Behind the Curve
Privacy advocates in the public sector have warned for years about how these apps track our location, with the data often sold for marketing and advertising purposes. The danger for the military is that the data could be used for far more deadly purposes.
Fitness apps are now among the egregious offenders of user tracking, according to a new study by Surfshark. It found that Strava is hardly alone in the data it gathers from users and then shares.
Tomas Stamulis, chief security officer at cybersecurity firm Surfshark, offered The National Interest a handful of tips on how users, including those in the military, should embrace such technology.
“Read privacy policies to understand how your data is being used,” Stamulis said, adding that users should limit app permissions to share only essential data. He further recommended that users opt for apps recognized for their transparency in handling user data, which can be certified by labels or other certifications.
“Use minimal personal information, create accounts with only essential information, and consider using a nickname instead of your full name,” Stamulis said.
However, being proactive in using fitness apps may not be enough, especially when using these devices on military bases or deployed warships.
“The behavioral gap is the real vulnerability,” said Gianchandani. “We have not caught up to the reality of how much we are broadcasting through everyday tools. This will remain the case until there are clearer gatekeepers, whether through regulation, platform accountability, or security protocols that treat consumer apps as potential threat vectors; we will keep seeing these incidents.”
About the Author: Peter Suciu
Peter Suciu has contributed to dozens of newspapers, magazines and websites over a 30-year career in journalism. He regularly writes about military hardware, firearms history, cybersecurity, politics, and international affairs. Peter is also a contributing writer for Forbes and Clearance Jobs. He is based in Michigan. You can follow him on Twitter: @PeterSuciu. You can email the author: [email protected].